What is Gremlin?
Gremlin’s Chaos Engineering tools allow you to safely, securely, and simply inject failure into your systems to find weaknesses before they cause customer-facing issues. It is a tool to perform system resiliency tests. It simulates real outages by injecting failures into the system to find weaknesses before they cause problems for the customers.
Gremlin has multiple failure injection strategies which can be broadly divided into four categories:
| Category | Impact |
| Resource | Starve your application of critical resources |
| State | Change the state of the environment your application is running within |
| Network | Simulate the inherently unreliable behavior of the network |
| Request | Impact individual requests as they hit the wire |
How to setup Gremlin in a Host Machine?
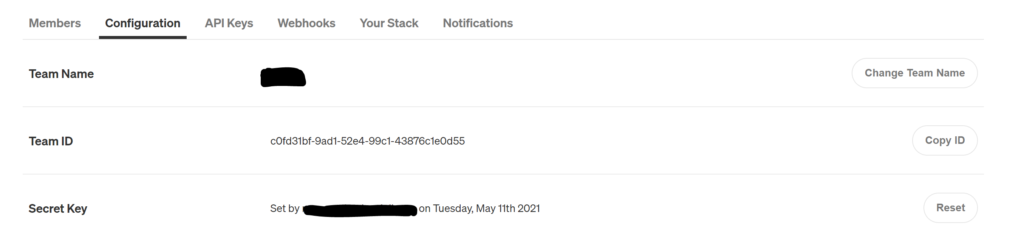
Gremlin comes with agents that needs to be installed onto your VMs or containers. Currently it supports Linux and Windows operating systems. Once you have procured your Gremlin license, you need to setup a Team and Users in the Gremlin portal. You need a Team ID and a secret to run your agent on the VM that will communicate with the Gremlin Portal. Gremlin supports multiple OSes and platforms like Kubernetes, docker, Linux and Windows.
How to do I execute an attack?
To run an attack, (lets, say a Shutdown attack which is under the State Category of Attacks)
First you need to install the Gremlin agent on to your VMs where you intend to run the specified attack. Once the agent is installed it will show up in the Gremlin Portal’s Client Page.

Clicking on the Attack Host button, you can trigger an attack in any one of the categories mentioned above.
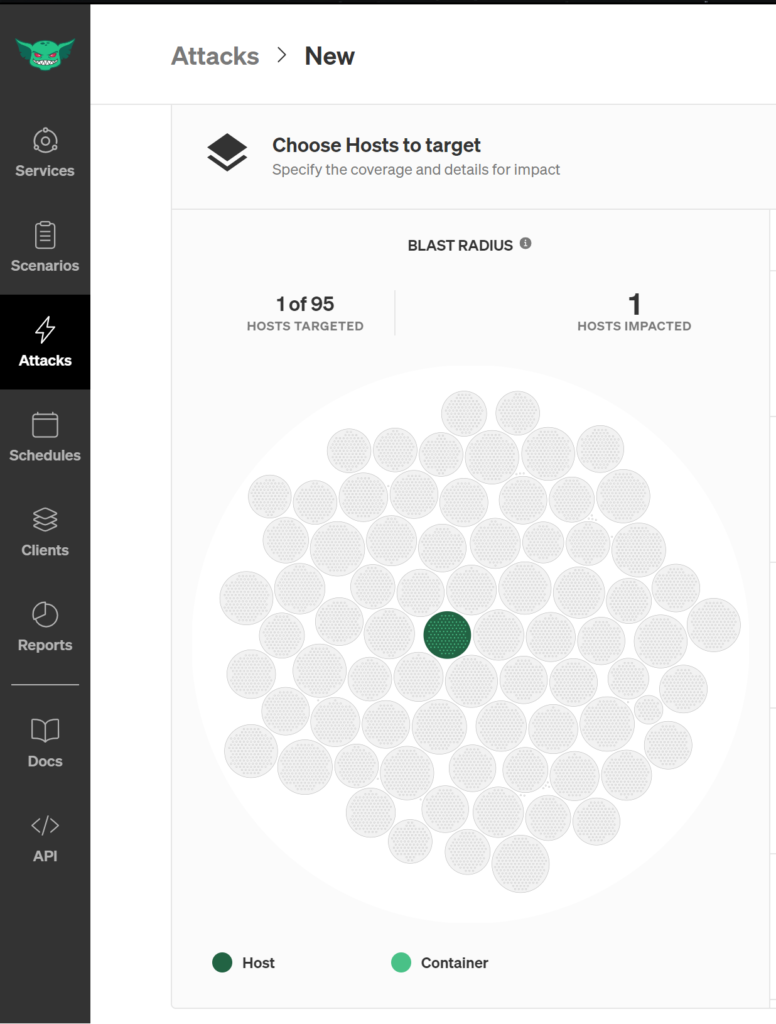
As you see the target is selected in Dark Green color.
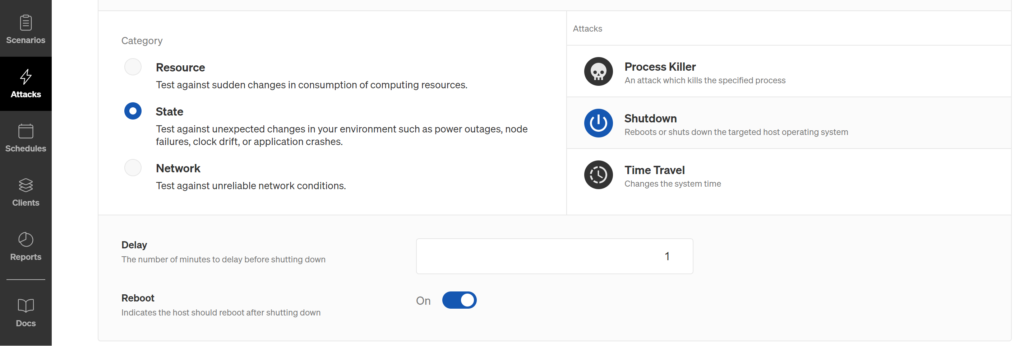
Next you need to select the type of attack, to do that select “Choose a Gremlin”. Select State category attack and then select Shutdown onto your right. Add in your delay in minutes and select the option whether you need to reboot your system after the shutdown takes place. If you don’t opt for reboot then you need to manually start your host once it shuts down triggered by the attack.
Once all the configs are selected, the last step is to click on Unleash Gremlin button… to trigger the attack.
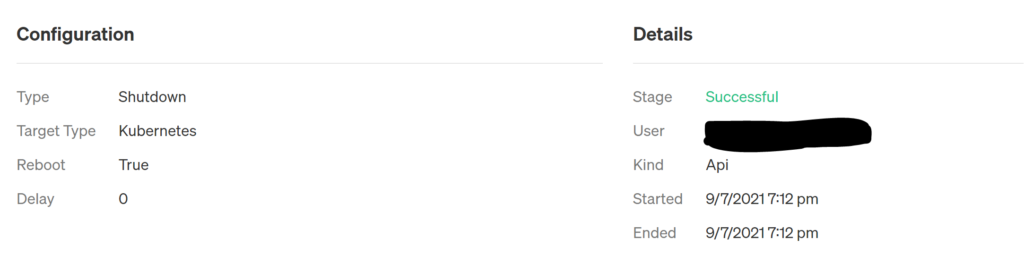
The attack will trigger and it will show you the status of the running attack, whether it started, halted, pending or successful stage, similar to the snapshot below:
Hope you find this quick intro helpful. In my next blog I’m going to show how can integrate Gremlin into your CI/CD Pipeline. With CI/CD integration you can automate the end to end process of injecting failures into your system and check for its Status.
Until then, happy exploring…


This is a great tip particularly to those new to the blogosphere.
Short but very accurate info… Thank you for sharing this one.
A must read post!